VERITI AND CROWDSTRIKE
Proactively monitor and remediate risk, vulnerabilities, and misconfigurations from the OS-level and up without disrupting business.
EXECUTIVE SUMMARY
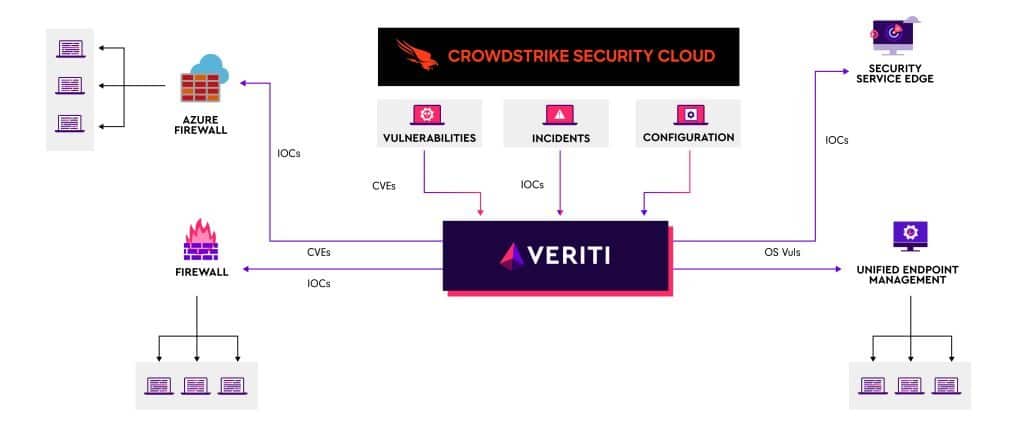
The integration of Veriti with CrowdStrike Falcon optimizes endpoint protection. This collaboration effectively utilizes EDR insights to implement virtual patches for both application and OS vulnerabilities, significantly reducing risks without necessitating restarts or resets. It streamlines OS patching processes to minimize business disruptions and features propagation of IoCs across all available security controls for a coordinated response. The solution also addresses feature-drift through real-time notifications, ensuring continuous, optimized security enforcement and reducing the likelihood of misconfigurations or outdated protections.
Solution Benefits
- Application Vulnerability Remediation
- OS Vulnerability Remediation
- Feature-Drift Notification
- Automated Threat Protection (IoC Management)
A PROACTIVE APPROACH WITH VERITI AND CROWDSTRIKE FALCON
Organizations today are challenged by the overwhelming number of security tools they have deployed. Oftentimes these tools are too disparate to efficiently respond to threats and swiftly address an increasing number of vulnerabilities detected by EDR systems (all without disrupting critical business operations). Application and OS vulnerabilities require immediate action to prevent breaches, yet traditional patching often necessitates system restarts, causing operational downtime. This creates a delicate balance between maintaining robust security and ensuring continuous business functionality.
Compounding this issue is the difficulty in accurately identifying genuine threats amidst a sea of false positives, along with the rapid evolution of cyber threats. Organizations often find themselves mired in manual, time-consuming processes, leading to delayed responses and potential security lapses. The pressing need is for a solution that not only quickly mitigates risks but also minimizes business impact, ensuring a resilient and efficient cybersecurity posture.
Veriti, integrated with CrowdStrike Falcon, addresses these challenges head-on. By automatically updating indicators from EDR incidents or recorded incidents from other security controls, Veriti triggers a coordinated response to stop the attacker dead in their tracks and keep them from coming back. By leveraging advanced analytics and EDR insights, this solution enables real-time virtual patching for both applications and operating systems, mitigating vulnerabilities without the need for disruptive restarts. It intelligently distinguishes between genuine threats and false positives, streamlining threat response and reducing manual workload. Additionally, the integration offers targeted, non-intrusive OS patches and proactive feature-drift notifications, ensuring security measures remain up-to-date without impacting business continuity.
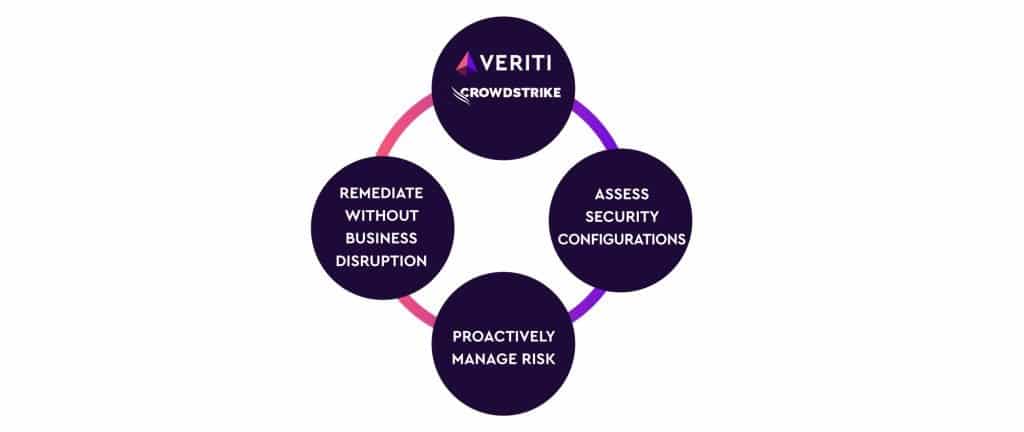
STRATEGIC ADVANTAGES SIMPLIFIED
Enjoy enhanced endpoint protection with minimal disruption: this Veriti-CrowdStrike integration offers swift vulnerability remediation, reduces false positives, and streamlines threat response, all while ensuring continuous business operations and significantly easing the cybersecurity management burden.
KEY FEATURES
Actionable Insights within Minutes by continuously analyzing your security controls, Veriti provides data-driven insights with automated root cause analysis that simplify investigations and reduces MTTR dramatically.
Optimize Resources- Maximize security efficiency with automated assessment and advanced security controls optimization capabilities.
Safe Remediation without Business Disruption- Filter out false positives and automatically remediate risk with confidence as every change is verified to not cause business disruption.
JOINT USE CASES
Vulnerability Remediation – Automatically identifies and remediates application vulnerabilities detected by EDR, applying relevant security layers to reduce risk without requiring application restarts. This ensures continuous application availability and security without operational disruptions.
Automated IOC Management – Easily add and manage threat intelligence feeds by automatically pushing updates to security tools to stay ahead of attackers. No need to manually update each tool. All IP Addresses, Files Hashes, Domains and URLs will be synced across the environment.
Feature-Drift and Compliance Assurance – The integration proactively identifies security enforcement reductions due to misconfigurations or outdated settings. It automatically adjusts settings, ensuring compliance and up-to-date security configurations, thus maintaining a consistent and strong security posture.




