Definition: Infrastructure Security in the context of cybersecurity refers to the practices and technologies used to protect the essential physical and digital infrastructure of an organization. This includes safeguarding critical systems, networks, hardware, and software that are vital to an organization’s operations and services. The aim is to ensure the resilience, reliability, and integrity of these infrastructural components against cyber threats, natural disasters, and other disruptions.
Infrastructure security forms the backbone of any organization’s cyber strategy, ensuring that both physical and digital assets are protected against evolving threats. While traditional security measures focus on reactive approaches, modern approaches emphasize proactive measures like continuous assessments and automated safe remediation to stay ahead of attackers. At the heart of this shift is Veriti’s Automated Security Control Assessment (ASCA), which transforms how organizations protect their infrastructure
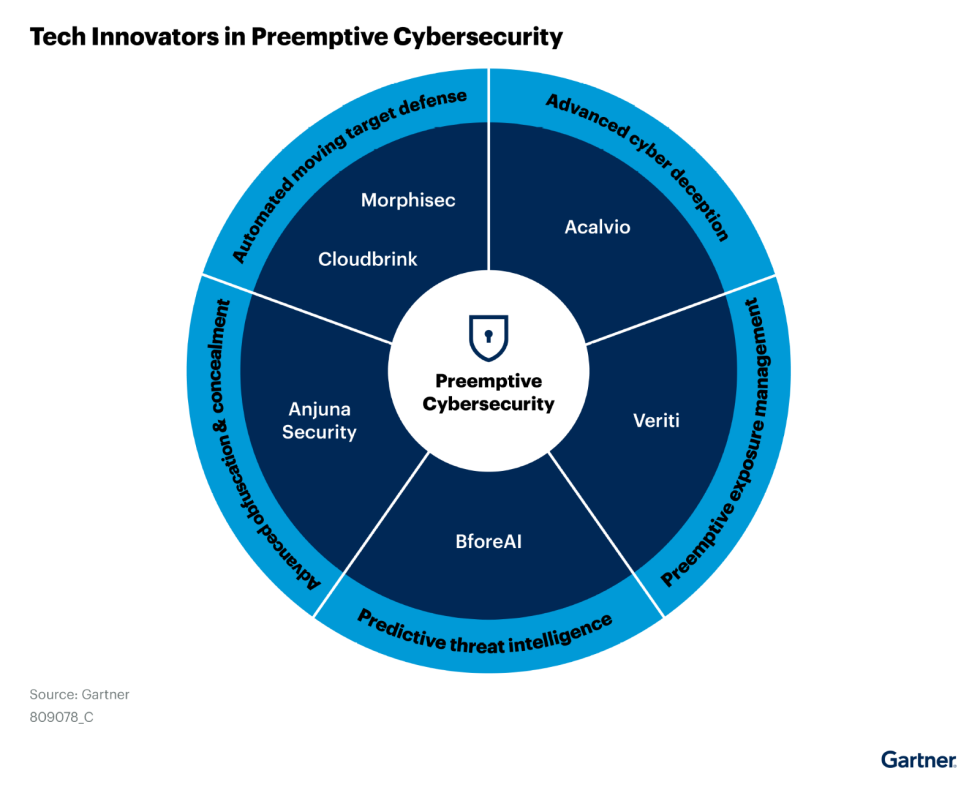
The security landscape is evolving, and traditional reactive strategies are no longer sufficient. Gartner’s 2025 Emerging Tech: Tech Innovators in Preemptive Cybersecurity highlights the need for organizations to shift towards proactive security measures. According to Gartner, by 2030, 75% of security solutions will include preemptive cybersecurity technologies to address threats before they escalate.
Veriti has been recognized as a Tech Innovator in Preemptive Cybersecurity, reinforcing its leadership in exposure assessment and automated remediation. This recognition validates Veriti’s approach to addressing security exposures before they become incidents—enabling organizations to strengthen their security posture with minimal disruption.
Key Elements of Infrastructure Security:
- Network Security: Implementing measures to protect data transmission, prevent unauthorized access, and secure network components.
- Physical Security: Protecting physical assets such as data centers, servers, and other hardware from unauthorized access, damage, or theft.
- Application Security: Securing applications from threats by ensuring they are developed, maintained, and used securely.
- Endpoint Security: Protecting devices connected to the network, such as computers, mobile devices, and IoT devices.
- Disaster Recovery and Business Continuity: Planning and implementing strategies to ensure business operations can continue and recover quickly in the event of a disruption.
- Importance of Infrastructure Security:
- Operational Continuity: Ensures that critical business operations are not disrupted by cybersecurity incidents or other threats.
- Data Protection: Safeguards sensitive and proprietary data from unauthorized access and breaches.
- Regulatory Compliance: Helps comply with various regulatory requirements that mandate specific security measures for critical infrastructure.
The Role of Exposure Management in Infrastructure Security
Traditional infrastructure security focuses heavily on detection and response. However, modern security strategies must go further—identifying and neutralizing threats before they can be exploited. Exposure management plays a critical role in this evolution by continuously monitoring and addressing vulnerabilities across IT environments.
Veriti integrates exposure management into infrastructure security by:
- Aggregating and analyzing security configurations across on-prem and cloud environments.
- Prioritizing vulnerabilities based on business and security impact, reducing time wasted on low-priority alerts.
- Applying safe, automated remediation to misconfigurations, vulnerabilities, and policy gaps—without disrupting critical infrastructure.
This proactive approach ensures organizations stay ahead of evolving cyber threats while maintaining operational continuity.
Continuous Security Control Assessments with Veriti
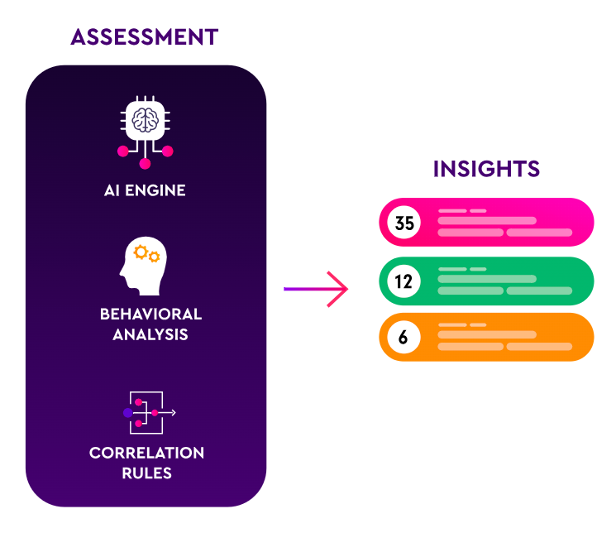
Strong infrastructure security starts with visibility. Veriti’s agentless approach, leveraging APIs, integrates seamlessly with existing security tools to conduct continuous ASCA. This eliminates the need for additional hardware or software while providing comprehensive monitoring of vulnerabilities, security gaps, and potential business disruptions. By consolidating data from Vulnerability Assessments (VAs), Breach and Attack Simulation (BAS) tools, and threat intelligence feeds, Veriti automatically pinpoints root causes of risks, ensuring targeted prioritization of threats.
Veriti Odin, an AI-driven assistant, empowers organizations with end-to-end visibility into their attack surface, spanning traditional and modern assets, including cloud environments, digital endpoints, and legacy systems. This comprehensive discovery ensures that security teams have a unified view of their infrastructure, capturing real-time insights into vulnerabilities across all asset classes.
Challenges in Infrastructure Security:
- Evolving Cyber Threats: Keeping up with the constantly changing nature of cyber threats and vulnerabilities.
- Resource Allocation: Effectively allocating resources between different aspects of infrastructure security.
- Complex IT Environments: Managing security in increasingly complex IT environments, especially with the integration of cloud services and IoT devices.
- Best Practices for Infrastructure Security:
- Regular Risk Assessments: Conducting periodic security assessments to identify and address vulnerabilities.
- Layered Defense Strategy: Implementing a multi-layered security approach to provide comprehensive protection.
- Continuous Monitoring and Incident Response: Establishing robust monitoring systems and a prepared incident response plan.
- Employee Training and Awareness: Educating staff about security best practices and potential threats to infrastructure security.
Prioritization: Targeting the Most Critical Risks
Veriti’s prioritization approach ensures that security teams focus on vulnerabilities with the highest risk and business impact. By incorporating metrics like CVSS and EPSS scores, Veriti identifies actively exploited exposures, layering in contextual intelligence from threat groups and affected assets. This real-time analysis not only prioritizes critical threats but also correlates them with operational data, making them immediately actionable.
Additionally, Veriti’s advanced IoC management aggregates and distributes IoCs across all security tools, ensuring countermeasures are deployed effectively. This unified approach enables organizations to allocate resources efficiently, addressing the most pressing vulnerabilities without unnecessary operational disruptions.
Preemptive Risk Mitigation with Veriti
Veriti enables preemptive risk mitigation by:
- Providing real-time threat identification and prioritization, ensuring security teams focus on the highest-risk exposures first.
- Leveraging compensating controls when patching is not an option, allowing organizations to secure vulnerable assets without downtime.
- Enabling agentless, API-driven integration across over 70 security tools, ensuring seamless infrastructure protection without deployment complexity.
With Veriti, organizations move from reactive security postures to proactive risk reduction, ensuring infrastructure security aligns with business continuity.
Mobilization: Efficient Remediation with Veriti
Effective security doesn’t stop at identification, it demands action. Veriti’s mobilization approach integrates seamlessly with ITSM, collaboration, SIEM, and SOAR platforms, streamlining the remediation process. Security teams can initiate actions directly within Veriti or through their preferred ITSM tools, ensuring that remediation workflows align with organizational priorities.
Veriti’s one-click remediation allows teams to automate routine processes, reducing manual intervention and improving response times. This ensures that remediation efforts are not only efficient but also consistent with business goals, minimizing downtime and operational impact.
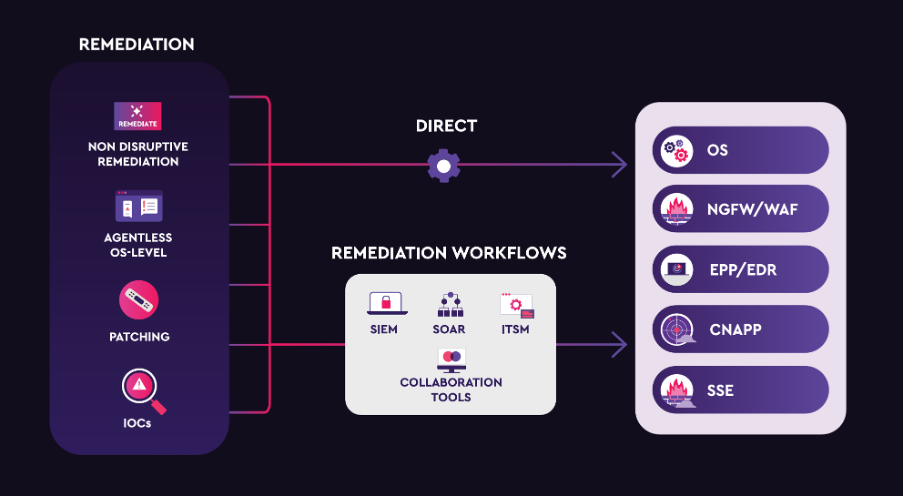
From Discovery to Remediation: A Unified Approach
Veriti ensures a seamless transition from discovery to remediation. By combining continuous assessment, intelligent prioritization, and actionable mobilization, Veriti enables organizations to address vulnerabilities comprehensively. This integrated approach reduces Mean Time to Remediate (MTTR), strengthens security postures, and ensures that critical business operations remain unaffected by cyber threats.
Veriti’s Role as a Tech Innovator in Infrastructure Security
Veriti’s recognition in the Gartner Emerging Tech: Tech Innovators in Preemptive Cybersecurity report underscores its leadership in proactive security. As attackers adopt generative AI and automated attack techniques, security teams must adopt preemptive defenses that neutralize threats before they escalate.
By integrating real-time exposure assessment, safe remediation, and security control enforcement, Veriti is redefining infrastructure security. Organizations that embrace preemptive cybersecurity will not only reduce risk but also gain a significant operational advantage in securing their critical assets.
The Future of Infrastructure Security with Veriti
Infrastructure security now demands a proactive, integrated approach that combines visibility, prioritization, and mobilization into one cohesive strategy. Veriti’s ASCA approach delivers on this promise, empowering organizations to secure their infrastructure with precision and confidence.




