The Veriti research team has analyzed the latest cloud vulnerabilities, revealing critical security risks, attack patterns, and real world exploitation cases.
Our findings highlight the top vulnerability categories, the most exploited CVEs, and the actors leveraging these weaknesses. In this report, we delve into key cloud security threats and provide insights on mitigating them.
Cloud Malware and Exploited Vulnerabilities
Cloud based applications and infrastructure are prime targets for attackers seeking to compromise sensitive data, disrupt operations, or deploy malware. Our research identifies some of the most exploited vulnerabilities and the techniques used by cybercriminals.
In cloud environments, the most common vulnerability types include:
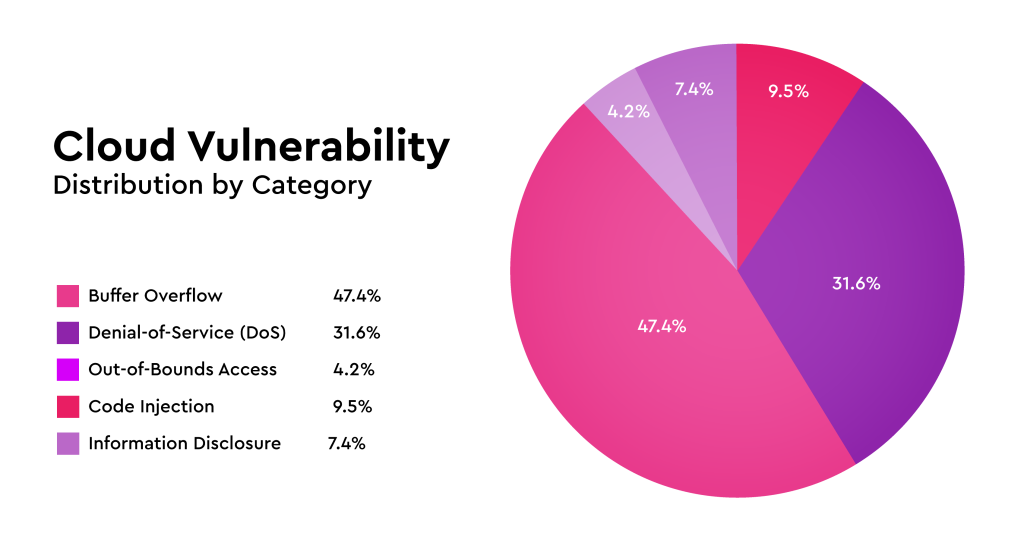
These categories represent a significant attack surface, with buffer overflow and DoS vulnerabilities being the most widespread.
Case Study: Jenkins Vulnerability (CVE-2024-23897)
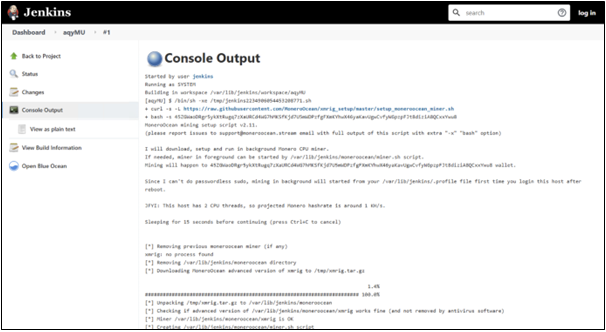
One of the most alarming vulnerabilities observed is CVE-2024-23897, which affects Jenkins 2.441 and earlier, as well as LTS 2.426.2 and earlier. This flaw allows unauthenticated attackers to read arbitrary files from the Jenkins controller file system via a command parser misconfiguration.
- EPSS Score: 96.67% (high likelihood of exploitation)
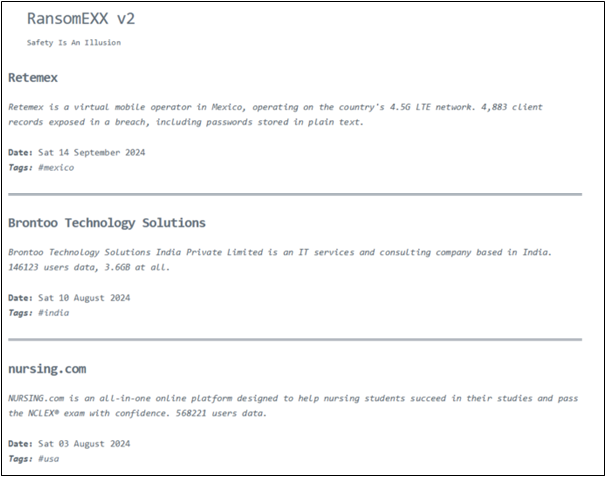
- Exploited by: Ransomexx ransomware group
- Real-World Impact:
- According to Juniper Research, the Ransomexx group has actively exploited this vulnerability in ransomware attacks against Indian banks.
- Veriti research identified 14,333 exposed Jenkins servers, with 6,495 EC2 instances vulnerable to this exploit.
- Attackers have already leveraged this vulnerability to deploy cryptominers on compromised servers.
Recommendation: Organizations should immediately update Jenkins instances and restrict access to CLI functionalities to mitigate risk.
Critical Veeam Backup Vulnerability (CVE-2024-40711)
Another critical vulnerability observed is CVE-2024-40711, affecting Veeam Backup & Replication software. This unauthenticated remote code execution (RCE) vulnerability allows attackers to execute arbitrary code by exploiting deserialization flaws in Veeam’s backup systems.
Why This Matters
- Impact: Attackers can gain full system control, manipulate data, and move laterally within networks.
- Ransomware Threat: Previous Veeam vulnerabilities (e.g., CVE-2023-27532) have been exploited by EstateRansomware, Akira, Cuba, and FIN7.
- Exposed Systems:
- Censys observed 2,833 exposed Veeam Backup & Replication servers, primarily in Germany and France.
- Not all are vulnerable, but the potential for exploitation is high.
Recommendation: Organizations must patch immediately, enforce strict network segmentation, and monitor for abnormal activity on backup servers.
Most Exploited CVEs in Cloud Environments
Veriti research analyzed the most exploited cloud vulnerabilities based on EPSS scores. Below are the top threats:
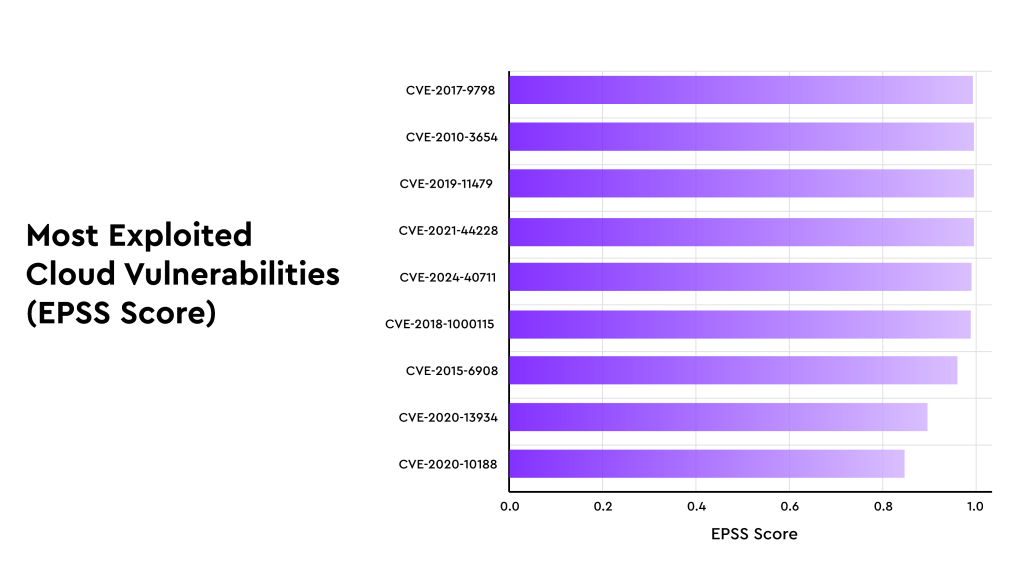
The presence of older CVEs (such as Log4j and Optionsbleed) highlights the persistent risk posed by unpatched legacy systems in cloud environments.
Conclusion & Recommendations
The latest Veriti research underscores the urgent need for proactive cloud security. With thousands of exposed and vulnerable systems, attackers continue to exploit high-risk CVEs, including Jenkins, Veeam, and Apache Log4j.
To protect against these evolving threats, organizations should:
- Patch critical vulnerabilities promptly to prevent exploits.
- Implement zero-trust principles, limiting access to cloud applications and infrastructure.
- Enhance monitoring & threat detection to identify malicious activity early.
- Harden cloud configurations, reducing unnecessary exposure to the internet.
- Conduct regular security assessments to uncover misconfigurations and vulnerabilities.
Cloud security is an ongoing challenge, but by adopting a proactive security strategy, enterprises can mitigate risks and strengthen their defenses against emerging threats.




