In recent research, Veriti has uncovered a range of advanced tactics cybercriminals are using to exploit operating systems, taking advantage of built-in functionalities to conduct malicious activities undetected. Operating System (OS) hardening, configuring and securing systems to minimize exposures, is critical to safeguarding an organization’s infrastructure. Veriti’s latest research shines light on how attackers like Magic Hound are exploiting these vulnerabilities and the steps organizations can take to mitigate these risks through effective OS hardening.
How Attackers Exploit OS Vulnerabilities
Veriti’s recent research reveals that cybercriminals are increasingly manipulating OS configurations, firewalls, and security settings to bypass detection and gain unauthorized access. Attackers leverage these OS features to disable protective protocols, conduct remote access, and manipulate system configurations for malicious gain. Here are multiple techniques Veriti has observed in recent attacks:
Manipulating Built-in Firewalls
One of the most common tactics Veriti’s research has identified is attackers modifying system firewall settings to allow malicious traffic and enable unauthorized access. By adding custom host rules, attackers allow malware to communicate externally and access compromised hosts remotely. This method, categorized by MITRE as T1562 – Impair Defenses enables attackers to disable firewalls or set specific rules that allow both inbound and outbound connections for malicious activities. This may take many forms, such as killing security software processes or services, modifying / deleting Registry keys or configuration files so that tools do not operate properly, or other methods to interfere with security tools scanning or reporting information. Adversaries may also disable updates to prevent the latest security patches from reaching tools on victim systems.
For example, Quasar RAT, a remote access trojan observed in Veriti’s analysis, modifies local firewall rules on Windows systems to maintain a persistent connection to the attacker’s control center. The image below shows how Quasar RAT alters firewall settings to bypass security controls.
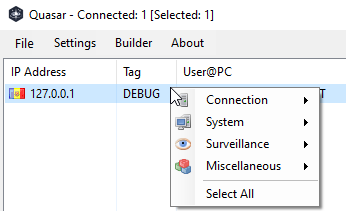
As seen in the sample, the RAT added 5 rules to the local windows firewall to achieve inbound and outbound remote access:
| C:\Windows\System32\cmd.exe” /k powershell New-NetFirewallRule -DisplayName “ngrok” -Direction Inbound -Program “C:\Users\<USER>\AppData\Roaming\Venom\Venom-ngrok.exe” -Action Allow & exit |
| C:\Windows\System32\cmd.exe” /k powershell New-NetFirewallRule -DisplayName “ngrok” -Direction Outbound -Program “C:\Users\<USER>\AppData\Roaming\Venom\Venom-ngrok.exe” -Action Allow & exit |
| C:\Windows\System32\cmd.exe” /k powershell New-NetFirewallRule -DisplayName “rdp” -Direction Inbound -Program “C:\Users\<USER>\AppData\Roaming\Venom\rdpinstall.exe” -Action Allow & exit |
| C:\Windows\System32\cmd.exe” /k powershell New-NetFirewallRule -DisplayName “vnc” -Direction Inbound -Program “C:\Users\<USER>\AppData\Roaming\Venom\Venom-winvnc.exe” -Action Allow & exit |
| C:\Windows\System32\cmd.exe” /k powershell New-NetFirewallRule -DisplayName “vnc” -Direction Outbound -Program “C:\Users\<USER>\AppData\Roaming\Venom\Venom-winvnc.exe” -Action Allow & exit |
Disabling Security Tools
Another alarming trend Veriti has observed involves attackers disabling or modifying critical security tools. For instance, Agent Tesla is known to disable Windows Defender by setting DisableRealtimeMonitoring to 1 within registry keys, allowing it to operate freely without interference.
Other actions taken by Agent Tesla to disable security features in Microsoft:
- Disabling Windows Defender’s AntiSpyware by modifying the DisableAntiSpyware setting.
- Disabling Real-time Monitoring by setting DisableRealtimeMonitoring to 1.
- Disabling Special Running Modes related to Windows Defender.
- Preventing Windows Defender from sending reports to Microsoft by disabling Spynet reporting and signature updates.
- Adding new registry entries under Windows Defender policies and setting them to disable certain protection mechanisms.
- Preventing the reporting of infection information.
A recent discovery of GU Loader via Check Point further underscores the risks, as it was found to deploy payloads undetected by disabling local protections upon installation. GU Loader’s sophisticated evasion techniques emphasize the need for strict OS configurations to block such alterations.
- GuLoader is a prominent shellcode-based downloader that has been used in a large number of attacks to deliver a wide range of the “most wanted” malware.
- GuLoader has been active for more than three years and is still undergoing further development. The latest version integrates new anti-analysis techniques, which results in it being significantly challenging to analyze. New GuLoader samples receive zero detections on VirusTotal, ensuring its malicious payloads also remain undetected.
As seen in the sample, the malware created two rules (allowing inbound and outbound connections on pre-define high-ports) to allow the remote attacker to communicate with the installed malware without being blocked by the local firewall.
| powershell.exe -Command |
| New-NetFirewallRule -DisplayName ‘Remote Management Access TCP’ -Direction Outbound -Protocol TCP -LocalPort 9001-9005 -Program C:\Windows\System32\Persistence\nc64.exe -Action Allow; |
| New-NetFirewallRule -DisplayName ‘Remote Management Access TCP’ -Direction Inbound -Protocol TCP -LocalPort 9001-9005 -Program C:\Windows\System32\Persistence\nc64.exe -Action Allow; |
Abuse of Safe Mode for Persistent Access
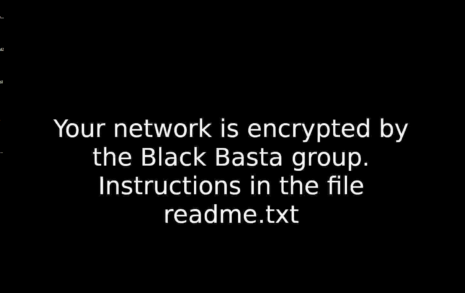
In our analysis, Veriti also noted the abuse of Safe Mode by Black Basta, a ransomware that relies on minimal driver environments to avoid security detection. By booting the infected system into Safe Mode, Black Basta minimizes the likelihood of detection from EDR and other security tools. The image highlights how Black Basta alters boot configurations for this attack.
Black Basta is ransomware written in C++ that has been offered within the ransomware-as-a-service (RaaS) model since at least April 2022; there are variants that target Windows and VMWare ESXi servers. Black Basta operations have included the double extortion technique where in addition to demanding ransom for decrypting the files of targeted organizations the cyber actors also threaten to post sensitive information to a leak site if the ransom is not paid.
As see in the sample, the malware is trying to set safe mode boot:
C:\Windows\SysNative\bcdedit.exe /set safeboot network
C:\Windows\SysNative\vssadmin.exe delete shadows /all /quiet
C:\Windows\system32\cmd.exe /c C:\Windows\SysNative\bcdedit.exe /set safeboot network
C:\Windows\system32\cmd.exe /c C:\Windows\SysNative\vssadmin.exe delete shadows /all /quiet
C:\Windows\system32\cmd.exe /c C:\Windows\System32\bcdedit.exe /set safeboot network
C:\Windows\system32\cmd.exe /c C:\Windows\System32\vssadmin.exe delete shadows /all /quiet
C:\Windows\system32\cmd.exe /c bcdedit /set safeboot network
Magic Hound Attack and OS Exploits
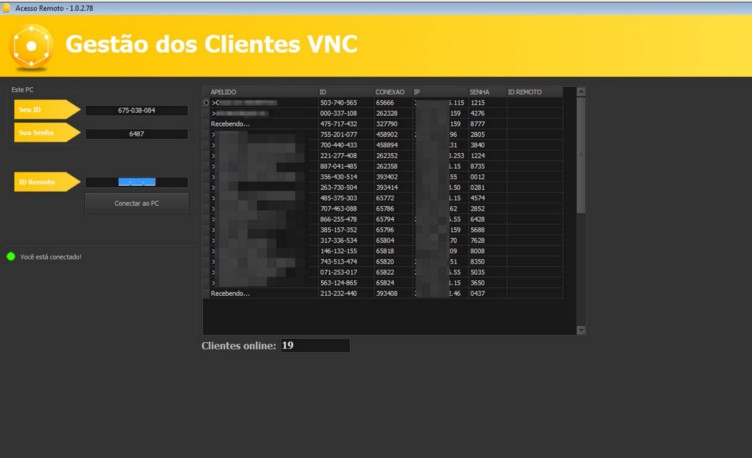
Another recent campaign tracked by Veriti is Magic Hound, a group known for targeting Middle Eastern organizations with advanced techniques. Magic Hound exploits OS-level vulnerabilities to evade detection, disabling local protections and manipulating system configurations. This group has gained access to sensitive networks by leveraging OS-level vulnerabilities, deploying malware that modifies system settings for persistence and lateral movement. As Magic Hound continues to evolve its tactics, it highlights the critical need for comprehensive OS hardening to preemptively close these attack vectors.
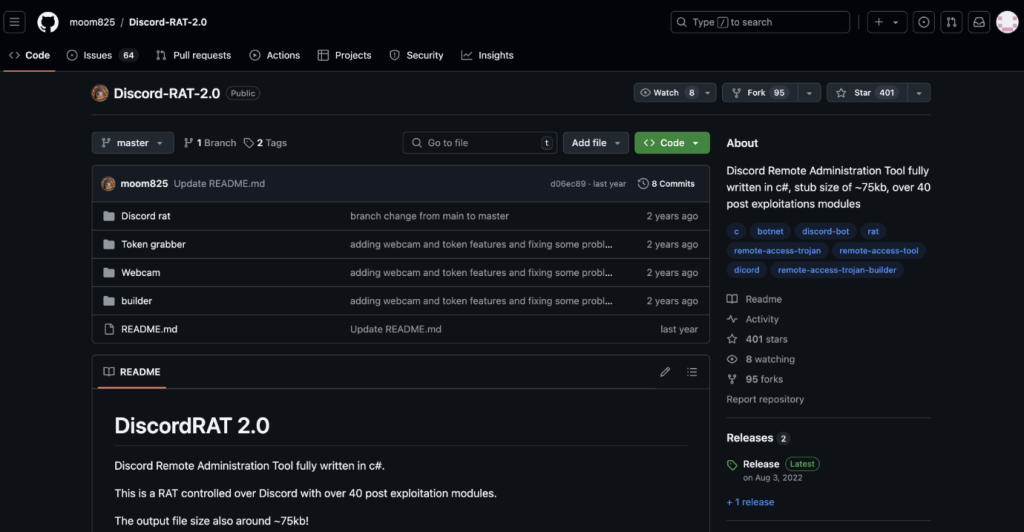
- DiscordRAT: A remote access trojan that uses Discord as a command-and-control center to manage compromised systems remotely. By implementing strict firewall configurations that limit access to management ports, organizations can disrupt DiscordRAT’s communication channels. The image shows firewall settings designed to block DiscordRAT’s primary communication methods.
In the sample, we can see that the rule that is embed into the local firewall is to allow inbound connection in SSH from a remote host.
“cmd.exe” /C New-NetFirewallRule -Name “SSH” -DisplayName “OpenSSH Server (sshd)” – Enabled True -Direction Inbound – Protocol TCP – Action Allow – LocalPort 22
- HydraPOS: Initially designed to capture payment data, HydraPOS has evolved to target e-commerce credentials. Registry hardening helps prevent unauthorized modifications, protecting against settings manipulations that could disable security tools. The images demonstrate a secured registry structure that protects against these attacks.
OS Hardening by Veriti
Given the growing sophistication of attacks observed in Veriti’s research, OS hardening is crucial for reducing the risk associated with these tactics. The following OS hardening capabilities can significantly strengthen security defenses and limit the impact of malicious activities:
- PROACTIVE, AGENTLESS OS-LEVEL REMEDIATION
Safeguard systems without the need for agents, additional files, or scanning—directly at the endpoint.
- SEAMLESS AND NONDISRUPTIVE REMEDIATION
No downloads, no system restarts, no downtime—just simple, secure remediation.
- COORDINATED REMEDIATION ACROSS LAYERS
Remediation options that span across the entire security stack, ensuring comprehensive protection.
Unlocking the Core: Insights and Actionable Steps from Veriti’s Research
Veriti’s research into OS vulnerabilities and the tactics of groups like Magic Hound reveal the critical need for a OS hardening strategy. With attackers leveraging every possible OS functionality to gain unauthorized access and persistence, organizations must establish comprehensive OS hardening protocols. From securing system configurations to enforcing Safe Mode restrictions, OS hardening serves as an essential shield against modern cyber threats.
For more information or to see Veriti in action, reach out for a demo today.




