Proactive and preemptive security strategies are no longer just an option—they’re essential. Gartner has just released its latest report on Emerging Tech: Security — Top Trends in Preemptive Cyber Defense, in which it is mentioned, “Preemptive exposure management (PEM) provides a preattack security strategy to continuously discover exposure points and remediate to strengthen an organization’s security posture in advance of an attack. This is foundational to an overall effective PCD program.”
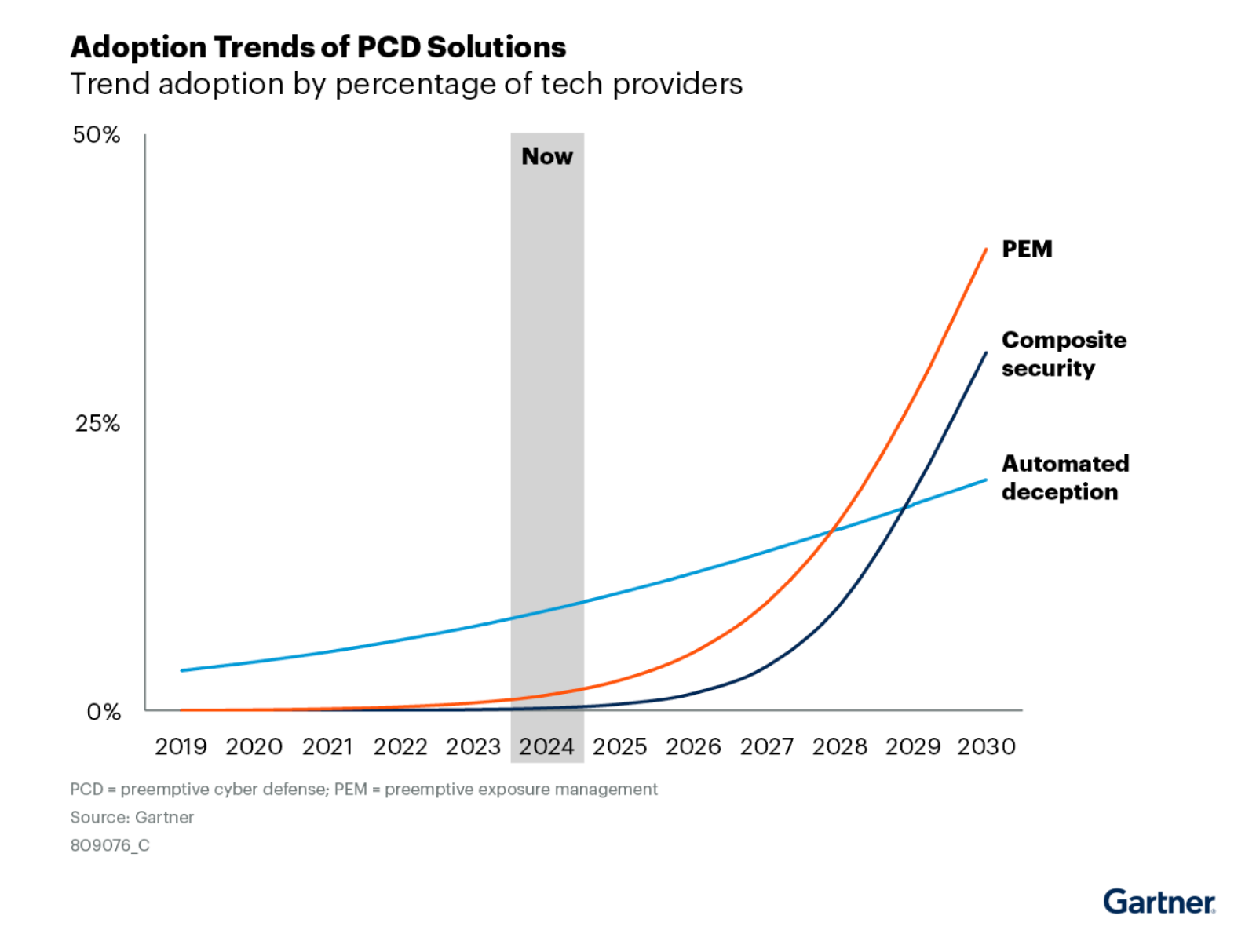
According to Gartner, “The dynamic nature of PCD to deceive, mask or mitigate exposures as they appear requires a significant amount of positive evidence with limited impact on business operations and a high degree of efficacy. As with any other emerging innovation, this will take time and there will be no linear adoption due to variances in budget, willingness to invest in emerging capabilities, or mature security operations beyond minimum viable security operations. Arguably, PCD is in the early stage of adoption and innovation. It is expected to be a few years before the majority of organizations start to adopt PCD solutions”, shown in Figure 1 of the report.
Gartner mentions that “By 2030, 60% of exposure management tasks and remediation will be automated, up from 10% today.”
This staggering growth shows the increasing reliance on automation in cybersecurity, as manual processes become too slow and inefficient to keep up with the rapidly changing threat landscape. PEM is enabling organizations to shift from being reactive to proactive, putting them ahead of potential attackers by identifying and fixing vulnerabilities before they can be exploited.
Veriti Mentioned as a Example Vendor for Preemptive Exposure Management
We are proud to announce that Veriti has been mentioned by Gartner as an example vendor for Preemptive Exposure Management. We believe that this recognition reinforces our position as a leader in providing proactive security solutions designed to help organizations manage their exposure and remediation of risks in real time.
Gartner’s report definition:
“Preemptive exposure management (PEM) provides a preattack security strategy to continuously discover exposure points and remediate to strengthen an organization’s security posture in advance of an attack.” We think that this aligns perfectly with Veriti’s core mission of proactive threat exposure management.
Preparing for the Automation Revolution in Exposure Management
As Gartner notes, “By 2030, 60% of exposure management tasks and remediation will be automated, up from 10% today.” The rapid increase in automation reflects the need for faster, more efficient ways to manage security risks. Manual processes, which were once the standard, are becoming outdated in the face of increasingly sophisticated cyberattacks.
At Veriti, we recognize the importance of automation in reducing time-to-remediation and ensuring consistent, reliable protection across an organization’s infrastructure. Our platform leverages advanced automation capabilities to continuously assess an organization’s exposure to threats and automatically mobilize remediation actions when exposures are identified.
Veriti’s Exposure Assessment and Remediation Solution: Leading the Future of Cyber Defense
Veriti’s exposure assessment and remediation solution is primed for the increasing adoption of preemptive cyber defense technologies. Our platform integrates seamlessly with existing security infrastructures to provide a comprehensive view of your organization’s security posture. Through continuous monitoring and safe remediation, Veriti helps organizations stay one step ahead of attackers by addressing vulnerabilities and misconfigurations before they can be exploited while prioritizing all remediation efforts based on available compensating controls.
Our solution is built to support the key elements of Preemptive Exposure Management, including:
- Continuous Discovery: Veriti continuously scans your environment to identify potential exposure points and vulnerabilities across your entire digital ecosystem.
- Safe Remediation: Veriti ensures that exposure points are addressed quickly and efficiently, reducing the risk of attack.
- Real-Time Threat Visibility: Our solution provides real-time insights into your organization’s security posture.
- Seamless Integration: Veriti integrates with your existing security tools and systems, ensuring that your organization can leverage its current infrastructure while enhancing its exposure management capabilities.
The Future of Preemptive Cyber Defense
As organizations continue to evolve their cybersecurity strategies, the importance of preemptive solutions like PEM cannot be overstated. By automating exposure management and mobilizing remediation, Veriti helps organizations achieve a higher level of security without the need for constant manual oversight. According to us our recognition by Gartner as an Example vendor in this space underscores our commitment to delivering innovative solutions that address the real-world challenges faced by today’s businesses.
Looking ahead, the stakes will only get higher. As cyber threats become more sophisticated and widespread, organizations must embrace preemptive solutions that allow them to anticipate and safely remediate exposures before they escalate into major security incidents.
As the report notes, “Preemptive exposure management (PEM) provides a preattack security strategy to continuously discover exposure points and remediate to strengthen an organization’s security posture in advance of an attack.”
With Veriti at the forefront of this movement, we are committed to helping organizations transform their security operations and embrace the future of preemptive cyber defense.

Gartner subscribers can access the full Emerging Tech: Security — Top Trends in
Preemptive Cyber Defense report on the Gartner website.
Gartner, Emerging Tech: Security — Top Trends in Preemptive Cyber Defense, John Collins, Luis Castillo, Isy Bangurah, Walker Black, 4 September 2024
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Gartner does not endorse any vendor, product, or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designations. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.




